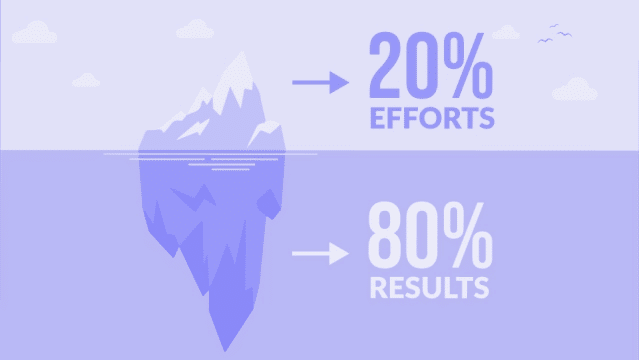
Have you ever heard about Pareto’s law? A curious rule of thumb says that 20% of the work done will bring 80% of the result, and vice versa — the remaining 80% of the work will bring only 20% of the result. Various experts in their field try it on themselves. Economists say that 20% of the population consumes 80% of the resources created, and system administrators that if 20% of errors are corrected in Windows, 80% of problems will disappear. Our security team engineers apply it to the total number of leaks. It turns out that 80% of software vulnerabilities are accidental, and 20% are intentional. Let’s talk about how we use Pareto Principle in the cyber defenses field.
What is the Pareto Principle?
The Pareto Law (PP) or the 80/20 principle states that only 20% of efforts give 80% of the result, and the remaining 80% of efforts give only 20% of the result. The mathematical dependence that formed the basis of PP was derived by the Italian economist and sociologist Vilfredo Pareto back in 1897.

For a generation, the importance of PP has been underestimated. Despite the fact that a number of economists, including American ones, realized the importance of this law, it was only after the Second World War that two people simultaneously, but independently of each other, began to demonstrate to the world what the PP is capable of.
In 1949, Harvard philology professor George C. Zipf discovered the law of least effort, which, in essence, was a rediscovery and detailed substantiation of PP. Zipf’s law stated that resources (people, goods, time, knowledge, or any other source of product) self-organize in such a way as to minimize the work expended. Therefore, approximately 20% of any resource provides for the implementation of 80% of the activities associated with this resource. In order to demonstrate the constant recurrence of this pattern of imbalance in various fields, Zipf looked at population statistics, the field of philology, and the dynamics of the industry.
Another pioneer in the practical application of PP was the American engineer Iosif Yuran, born in 1904 in Romania, a recognized quality guru; this man stood at the origins of the quality revolution of 1950-1990. He proclaimed the Pareto law (or, as he sometimes called it, “the law of the decisive few”) as synonymous with finding ways to improve product quality.
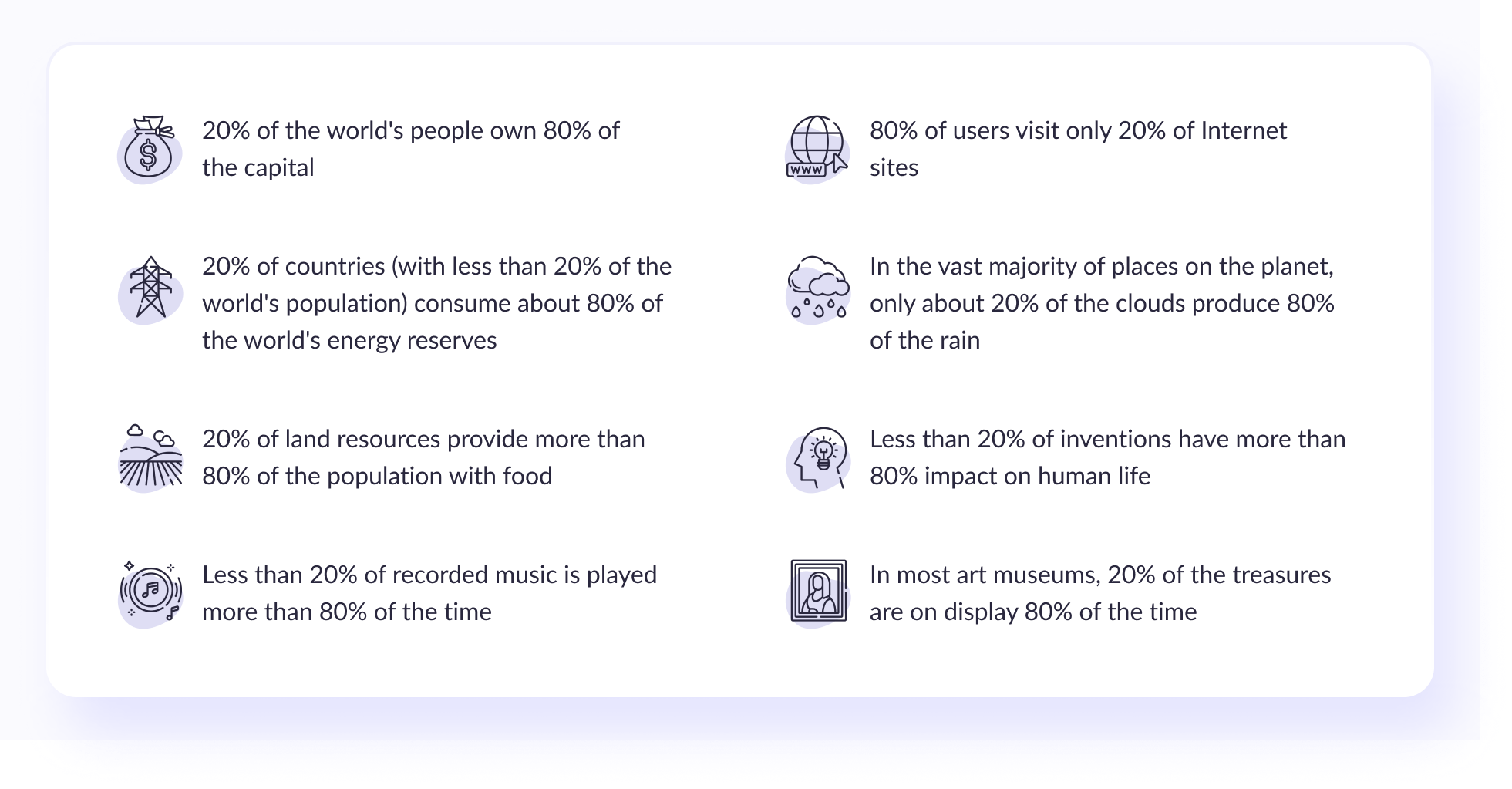
In his opinion, the observance of this law is very common in various areas, for example:
Example of the Pareto Principle
Everyday situations show that most people on the planet wear only 20% of the clothes that they have in their wardrobe 80% of the time.
Pareto’s law in life extends to reading books, as well as to the choice of a certain kind of literature. It has been proven that 80% of all books that a person has read in his life did not give him any useful information, but, on the contrary, affected the deterioration of vision and led to a waste of time. Only 20% of the literature read gives a person 80% of all the new knowledge and skills they successfully apply in everyday life.
Criminals are a vivid example in society — 20% of all convicts and prisoners in the world committed 80% of all crimes.
In marketing and sales, the Pareto Principle is best known for its formulation that 80% of profits come from 20% of customers. At the same time, 80% of sales come from 20% of products.
In life, it is necessary to set the three most productive hours in a day, during which a person will be able to perform up to 80% of all planned activities with the best result.
Subscribe to our newsletter
Pros and Cons of the Pareto Principle
Criticism of the Pareto principle is more related to mathematical calculations: the real distribution of the effectiveness of efforts leading to a result can be anything and not necessarily 20/80; the distribution can change significantly if the selected values are grouped in a different order.
Another “pitfall”: the properties of the system are determined by a certain set of parameters, the contribution of each of which to a specific property can vary significantly. By optimizing the system with an eye only on the Pareto rule, you can get into trouble by getting rid of an insignificant parameter in one property but decisive in another. In some cases, especially in the service sector, it is impossible to organize activities so as not to expend energy on 80% of rarely requested options or other inefficient aspects of the activity. There is a saying in the scientific community: ”20% of scientists make 80% of discoveries and inventions that would be impossible without the efforts of the remaining 80% of scientists.”
Advantage Of Security Principle 80/20
- Simplicity, ease of use: easy to implement, easy to use for analysis;
- Memorable, capacious wording;
- A wide range of problems that can be analyzed using the Pareto principle and find a solution;
- Really works in most cases;
- Capacious tool for demonstrating to management, customers, or anyone else the results of the analysis;
- Convenient to implement in basic programs, no need for additional software.
Cons
- There are areas in which the Pareto principle does not work: most often, those that require consistent work in “portions” every day. For example, when building a road, you cannot build 80% of the road in 20% of the working time — you must invest a little every day and build the entire road, and not just 80%. The same applies, for example, to writing a book or scientific work — for example, a diploma.The Pareto rule is not always accurate. The principle (more in less) is preserved but finds a different numerical expression, for example, 90/10, 70/30.
- Excessive categorically. For example, while implementing the Pareto principle in business, you must analyze the employees who work for you, identify the 20% that bring 80% of the profit, and get rid of the remaining 80%.
The Pareto Principle in Detection Cyber Security Incidents
It is challenging to deal with intentional leakage and have a high level of cyber resilience. Information is “leaked” either because of money or personal motives. Accidental leaks most often occur due to inattention or due to the illiteracy of employees. For example, they use the name of the wrong function in software development. Sometimes such cases lead to very ironic consequences. For instance, in the State of Detroit, the police department accidentally sent out a file with uniform sizes not only for male police officers but also for women, with all the data on the volume of the chest or waist. Many recipients noted that police officers of both sexes love donuts. At times, the consequences can be fatal, as was the case when, as a result of treacherous negligence, ten parcels were sent from Utah with anthrax spores.
In a large company, there are several ways to set up security controls and protect yourself from the inattention of employees. First, you need to do educational work about critical security flaws and security resources during the discovery phase. It is rightly said that ”forewarned means protected,” and the performance of companies that apply this rule is a prime example.
The second stage of protection is the use of DLP systems. It passes data streams through it, filtering data by certain keys. When the system detects sensitive information, an active code is triggered as threat information, which blocks data transmission. All these methods are good in their way in different systems, and have pros and cons, but what does the Pareto principle have to do with it, you ask? With that, there is another interesting way to deal with leaks.
A month ago, the Dmail extension appeared on the network, which allows you to block access to a letter even after it has been sent. For Gmail users, it has a built-in timer function that allows you to block a letter after a specified time after sending; it can be hours and days, and weeks. Curiously, Google recommends this service itself.
Returning to the field of information security (IS), it should be noted that according to various estimates of experts (including according to NIST — the National Institute of Standards and Technology of the USA), the main cause of damage to electronic information in the late XX — early XXI century in about 75% of cases was unintentional human error. In other words, the share of qualified personnel working in information security was about 20%.
It is known that over the past ten years, the annual volume of spam in electronic mailboxes around the world was ~80%, i.e., on average, users only received about 20% of the emails they were interested in when they used email.
According to Western experts, the leakage of 20% of commercial information in most cases leads to the the company’s bankruptcy. In other words, 80% of commercial information is of no interest to anyone, including the firm’s competitors.
As you know, the main perpetrators of computer crimes in ~80% of cases are employees of the organization, i.e., the number of loyal employees who comply with all safety standards and rules adopted by the company is ~20% of the total number of the company’s employees.
Based on the above, the following hypotheses can be formulated:
- 20% of financial resources for information protection in information and telecommunication networks and systems will be able to provide an 80% level of information protection in it;
- at each level of IS provision (legal, administrative, software and hardware, etc.), only 20% of the components of the corresponding level function effectively;
- of the entire spectrum of IS threats, about 20% of them are dangerous for the systems and networks of an organization;
- of all employees of the information security activities of various organizations, only about 20% of their total number function effectively;
- 80% of the encryption algorithms used are not cryptographically strong;
- 20% of the means and methods used to ensure the IS of the protected object ensure the achievement of an 80% level of information protection in the system;
- the proportion of unsuccessful attacks by intruders on their chosen information processing systems is about 80%;
- of all security personnel, only 20% of them provide 80% of the level of information protection.
Conclusion
Unfortunately, there’s no single formula to win the battle against cybercrime. However, the Pareto Cybersecurity 80/20 Principle provides practical guidance on how IT leaders can deal with this issue efficiently. They need to shift efforts and resources toward the threats that pose the greatest threat before tackling those with a lower impact on the business. You still have to establish the appropriate measures for the remaining cyber risks. But at 80 percent, the cybersecurity 80/20 rule means you’ll have covered all key bases.