One of the most pressing issues today is cyber security. The world has been dealing with a spree of online attacks and breaches of security protocols. Hackers shut down a power grid in Ukraine, stole personal information from health care companies, and even infiltrated the White House's system.
Understandably, cyber security has suddenly become a top priority for developers. To reduce the impact of these attacks, developers are now incorporating better cyber security measures into their applications.
This article explores the latest security breaches, cyber security trends, and how to stay protected from unwanted attacks.
Read in this post:
The Pareto Principle in Security
 Systems can never be 100% secure because any form of user input is seen as a potential threat and access to the internet.
Systems can never be 100% secure because any form of user input is seen as a potential threat and access to the internet.
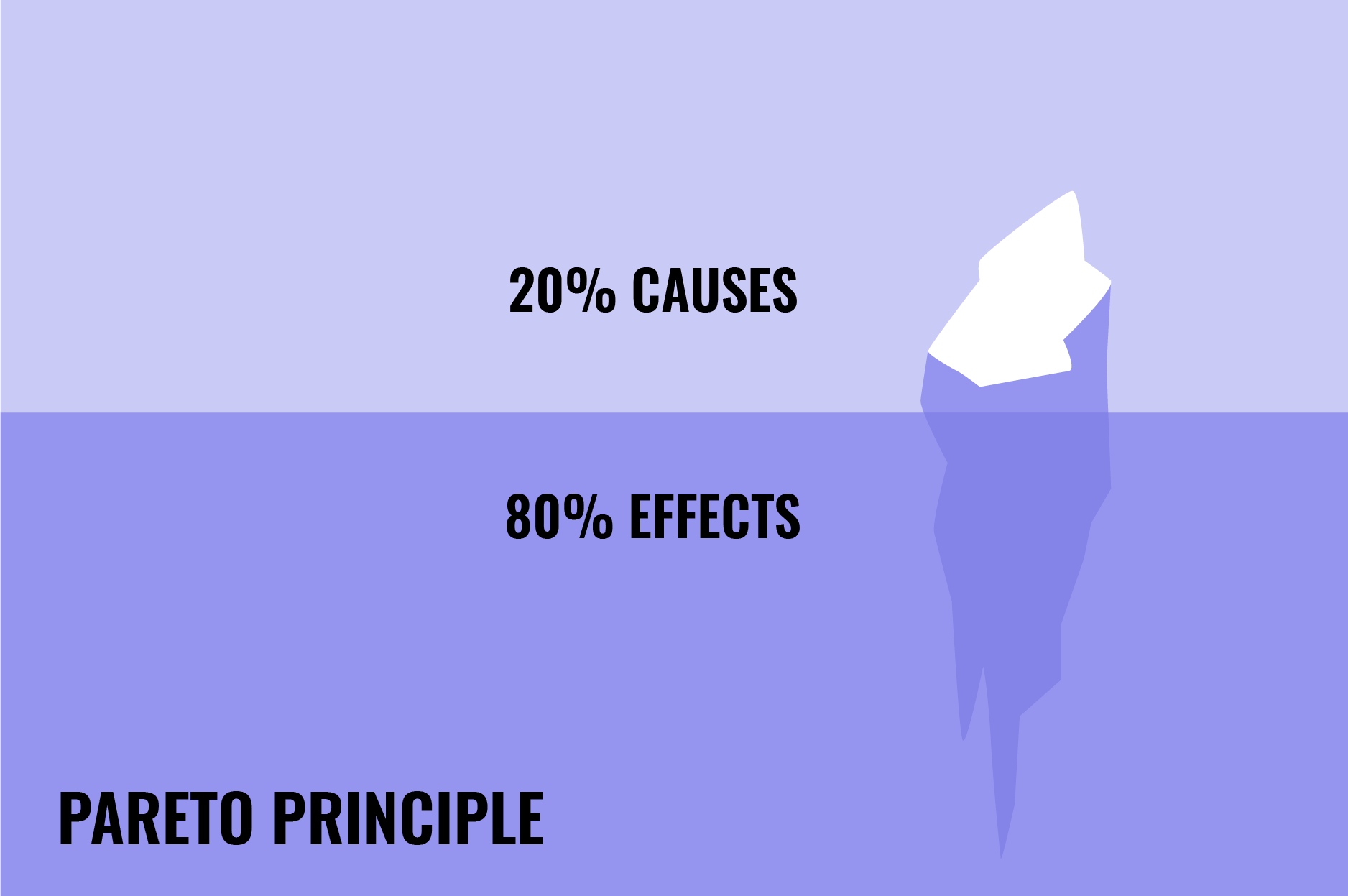
One of the most common cyber security principles is Pareto's Principle—also called the 80-20 rule. This principle states 80% of the effects come from 20% of the causes and explains how small portions of a system impact the rest of it.
In other words, correcting 20% of the most commonly reported problems in a program solves 80% of the errors. Simply implementing a few basic security precautions can make you significantly more secure.
Before we get to the latest trends in cyber security, we will first explore the top six breaches that occurred recently and their related trends.
Top 6 Security Breaches in 2022
The following list shows the six security breaches that contribute most to today's cyber security trends. We will then explore how developers can implement lessons from these breaches into their applications.
 1. Colonial Pipeline
1. Colonial Pipeline
One of the most devastating data breaches is the ransomware cyberattack on the Colonial Pipeline that triggered widespread gas interruptions and fuel supply panic. Because of the vast ransom paid by Colonial to hackers for the return of information, the Colonial Pipeline remains one of the most memorable moments in cyber attacks.
2. Kroger
Kroger Co. (Kroger) confirmed it had been impacted by a large-scale data breach at Accellion, a California-based third-party file-transfer service provider. The corporation claims it stopped using Accellion's products and services afterward and reported the matter to authorities.
3. Facebook, Instagram, and LinkedIn
A significant data breach at Socialarks exposed more than 400GB of personal information, including that of some high-profile celebrities and social media influencers. According to the cyber security team, the data was "scraped" from social media networks. The result: 200 million Instagram, Facebook, and Linkedin users' scraped data was exposed.
4. Volkswagen and Audi
Volkswagen and Audi, VW's luxury brand, were both struck by a data breach that exposed customer contact information and, in certain circumstances, personal information such as driver’s license numbers in the United States and Canada. It is believed that at least 3 million consumers or shoppers had their contact information stolen.
5. Bonobos
Bonobos, a well-known clothing store for men, experienced a massive data breach that exposed the personal information of millions of customers. How did the hacker get all this data? Simply by downloading a cloud backup of their database.
6. Parler
Parler is a not-so-well-known social media platform used to plan the storming of the United States Capitol. Security researchers leaked 70TB of Parler users' conversations, videos, and postings.
These breaches led to new cyber security trends to make systems, software, and applications safer than before. In the next section, we discuss the most effective methods used to protect software or any other IT solution.
How to Prevent Data Breaches and Protect IT Solutions
There are several basic steps to take to protect your IT solution from getting hacked.
Ensure that software is updated and patched regularly to avoid hackers exploiting security flaws.
Conduct vulnerability assessments to assess and remediate any modifications or new data security concerns.
Ensure that all personal data is encrypted, especially the data kept on employees' work laptops. Also, keep backups on remote services instead of backup tapes.
Train your staff and help them understand the importance of data security and the latest trends in cyber security. Also, make awareness of sensitive data and security a part of the company’s culture.
When collaborating with other firms that may handle your customers' data, ensure they have proper data protection mechanisms in place.
Have a third party do a risk assessment. This will provide an impartial and objective perspective on the present breach risks. A data security specialist can advise on the appropriate solutions for each company's unique needs to limit the danger of a data breach.
Now that you're more familiar with the most prevalent cyber security threats, let's proceed to the most popular trends in cyber security in 2022.
Cyber Security Trends in 2022
The latest trends in cyber security are meant to make things safer for consumers and businesses. In this section, we explore the most popular IT security trends in 2022.

1. Cloud
As data breaches get more sophisticated, cloud security becomes a necessity. If you own a business and collect customer information, then investigate the benefits of going onto "the cloud." Your company will benefit from a properly implemented IT solution on the cloud. The good news is that your customers will also appreciate it!
2. Artificial Intelligence Integration
Artificial intelligence (AI) can help fight cybercrime by detecting patterns of activity that indicate something unusual is going on. The machines learn from what they see, easily adapt to new situations, and are equipped with automatic threat detection. AI has powerful predictive capabilities that make it valuable, which is why more and more businesses are investing in these solutions.
3. Remote Work
Working from home introduces new cyber security threats and security vulnerabilities. When compared to centralized workplaces, home offices are frequently less secure. Many remote workers use two-factor authentication on their own devices, and they may have mobile app versions of instant messaging applications like Microsoft Teams and Zoom. Because of the blurring barriers between personal and professional life, sensitive information is more likely to slip into the wrong hands.
4. ZTNA
Zero trust network authentication (ZTNA) is a security strategy that rejects the traditional approach to authentication. By limiting remote access to sensitive data and lowering the likelihood of an attack, ZTNA has emerged as a more secure solution than VPNs.
5. Phishing Attacks
Phishing is a type of social engineering assault frequently used to obtain sensitive information from users, such as login credentials and credit card details. Phishing attacks are frequently employed as part of a bigger attack to obtain a foothold in business or governmental networks.
6. IoT Security
As the Internet of Things (IoT) keeps growing, so does its risk to cyber security. Most IoT devices are easy to exploit because they often use the same protocols used internally by business networks. They also have easily exploited vulnerabilities, which makes them attractive targets to attackers.
7. 5G
5G is expected to bring a range of security risks and vulnerabilities. More research is required to find out if they are precise. However, we know that the benefits of 5G connectivity will outweigh the potential risks.
8. Automation
Professionals and engineers are under increasing pressure to produce rapid and practical solutions in today's demanding work environment, making automation more useful than ever. Automation of data protection and cyber security solutions is another trend to watch.
9. Extended Detection and Response
Extended detection and response (XDR) collects and correlates data from several security layers, including email, endpoints, servers, cloud workloads, and networks. In addition to collecting all of this data, it also analyzes it to find suspicious activity.
Now that you are more familiar with the most popular information security trends and risks, the question remains—how do you protect yourself from them? The answer is in the next section!
The Open Web Application Security Project (OWASP) Top 10
The OWASP top ten is a standard awareness document for web application security and developers. It represents a general agreement on the most serious security threats to web applications.
Here are the top risks according to OWASP:
- Broken access control. Unauthorized users may gain access to important files or even user privilege settings due to broken access control issues.
- Cryptography failures. This type of failure frequently results in the exposure of sensitive data or the penetration of a system.
- Injection. When an attacker uses insecure code to introduce (or inject) their own code into a program, this is known as an injection.
- Insecure design. Discovered in 2021, design flaws are prone to making applications more prone to cyber-attacks.
- Security misconfiguration. Security configuration issues pose a significant threat because they allow attackers to gain quick and simple access to critical data and site areas.
- Vulnerable and outdated components. When components are not updated, they become increasingly susceptible to security issues.
- Identification and authentication failures. Hackers might access sensitive information without needing proper credentials due to identification and authentication failures.
- Software and data integrity failures. These issues allow hackers to obtain sensitive information, execute malicious code, or cause the application to act outside intended functionality.
- Security logging and monitoring failures. Attackers rely on the fact that many companies lack monitoring and have slower remediation timeframes to launch malicious attacks.
- Server-side request forgery. A web application that fetches a remote resource without validating the user-supplied URL is the most common cause of an SSRF fault.
With these risks in mind, you might ask how you check your app for vulnerability? The answer is simple with the help of pen testing, vulnerability scanning, and threat modeling. Let’s explore in more detail.
Penetration Test
Your best bet to determine your cyber security vulnerabilities is by using the services of penetration testers. Contact the professionals on the Geniusee team. They will run through your application with malicious intent, finding any security issues that may reveal themselves in real-world conditions.
The main benefit of pen testing is defining the vulnerabilities and finding the approaches to fix them. By running penetration tests, you will be able to:
- Determine and prioritize security threats.
- Manage vulnerabilities intelligently.
- Make use of a proactive security strategy.
- Check if existing security programs are operating and look for security flaws.
- Boost the company's security strategy's credibility.
- Comply with all regulatory requirements.
Here are several tips to make the most out of pen testing.
Test at least once a quarter or whenever your IT system undergoes a big update.
Define your company's security goals and assess your greatest risks.
Choose the tools your team can efficiently implement and utilize.
Don't just jump into pen testing. Define the scope and methodology of your tests.
Your penetration test results may require adjustments to your security infrastructure. Be open to new solutions.
Do thorough research on all your devices, applications, and databases.
Map out your biggest weaknesses and start your mediation efforts.
Always remain vigilant and consider every potential event and procedures that could put your organization at risk.
Vulnerability Scanner
There are two types of vulnerability scans:
- An authenticated security scan helps determine how secure a network is from an inside vantage point.
- An unauthenticated vulnerability scan examines the security of a target system from the outside.
The most common security scanners are:
- Acunetix
- beSECURE
- Burp Suite
- GFI Languard
- Frontline
- Nessus
- Nexpose
- Nmap
- OpenVAS
- QualysGuard
Threat Modeling
A threat model is a logical representation of all the data that influences an application's security. The main objectives of threat modeling are to identify security requirements, pinpoint security threats and potential vulnerabilities, quantify threats and vulnerabilities criticality, and prioritize remediation methods.
Threat modeling identifies the different threat agents that can affect a computer application or system. This strategy allows a company to put itself in the shoes of a malicious hacker to see how much damage it may cause.
Threat modeling consists of four stages:
- Diagram. What exactly are we attempting to build?
- Threat identification. What could possibly go wrong?
- Mitigate. What are we doing to protect ourselves against threats?
- Validate. Have we completed each of the preceding steps?
Conclusion
Cybercriminals are continuously looking for new ways to target and harm individuals and organizations in this age of accelerating digital change, which means cyber security challenges will continue to evolve.
In this article, we presented you with the most common cyber security trends and threats, as well as solutions that can help your company stay safe.
As Britney Hommertzheim, a rising trendsetter in technology and an IT security power player, said, “Cyber security leaders, we have to create our message of influence because security is a culture, and you need business to take place and be part of that security culture."





















